Table of Contents
In today’s hyper-connected digital world, computer security is critical. From personal data to enterprise systems, everything is vulnerable to cyber threats.. Cyberattacks are increasing every year and organisations are actively hiring professionals who understand security fundamentals.
This growing need makes it important to understand what are the core components of computer security and how do they protect digital systems from modern threats.
What Is Computer Security?
Computer security (cybersecurity) refers to the protection of computer systems, networks and sensitive data from unauthorised access, cyberattacks and digital threats. It is a crucial part of modern information security and data protection strategies.
It includes key areas such as the following:
- Data protection and privacy security
- Network security and threat prevention
- Application security and vulnerability management
- Information security practices and risk management

The cybersecurity goal is to protect sensitive data, ensure user trust and maintain system reliability, availability and digital security in an increasingly connected world.
Join Today For The Best Cyber Security Online Coaching
Tap Here
Main Components of Computer Security (CIA Triad)
The foundation of modern computer security and cybersecurity principles is built on the CIA Triad. There are three essential pillars that ensure complete data protection, information security and system reliability.
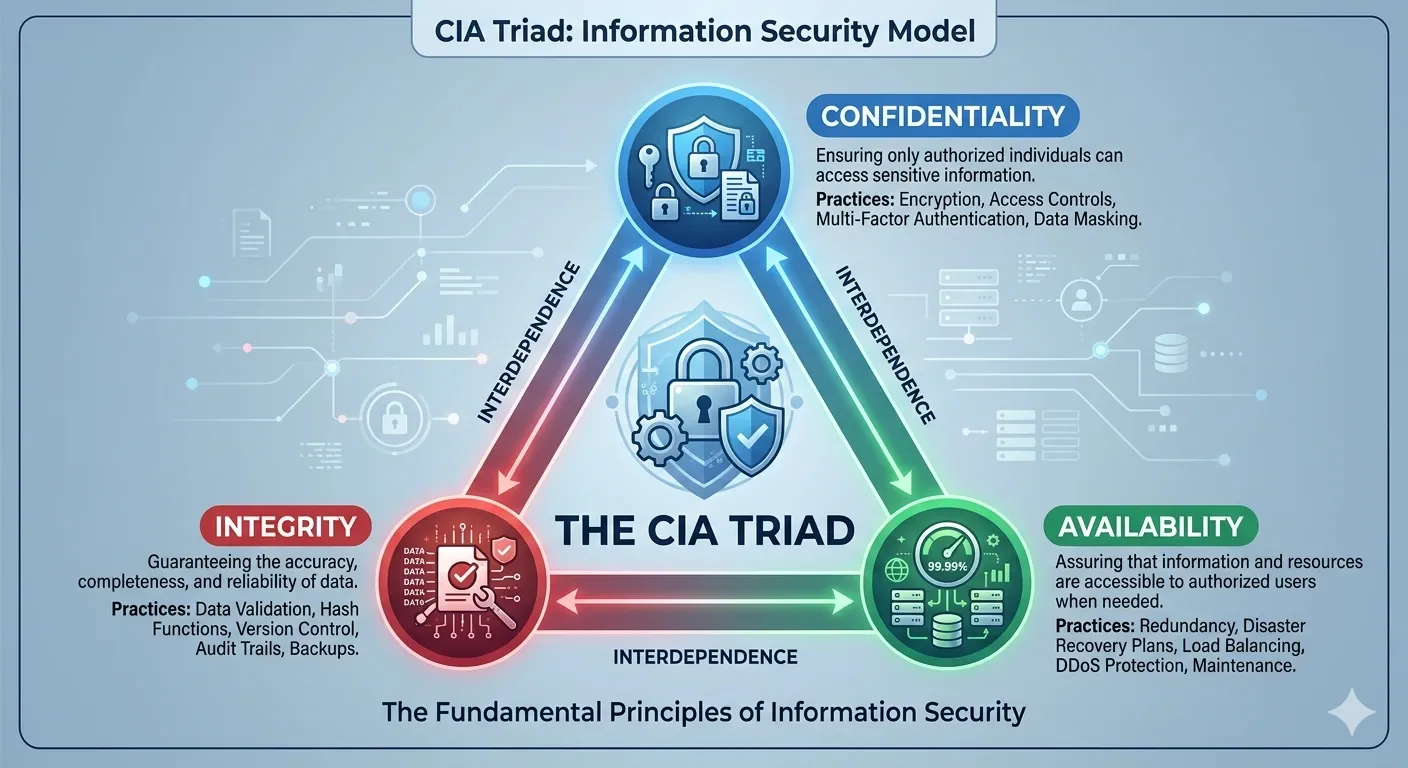
Image Source : Google Gemini
1. Confidentiality (Data Privacy & Protection)
Confidentiality ensures that sensitive data and information are accessible only to authorized users, protecting it from unauthorized access and cyber threats.
Key Concepts:
- Data encryption and encryption standards
- Access control systems and user permissions
- Strong password security
- Multi-factor authentication (MFA)
Example:
When you log into your banking or payment app, your data is protected using advanced encryption technologies, ensuring hackers cannot read or misuse your information.
Why It Matters:
Without strong data confidentiality measures:
- Personal and financial data can be exposed
- Businesses may lose customer trust and credibility
- Organizations can face serious cybersecurity risks
2. Integrity (Data Accuracy & Trustworthiness)
Integrity ensures that data remains accurate, consistent and unaltered unless modified by authorised users, maintaining trust in digital systems.
Key Concepts:
- Data validation and verification techniques
- Hashing algorithms and cryptographic checks
- Digital signatures and authentication methods
- File integrity monitoring systems
Example:
If financial or medical records are altered by unauthorized users, the system may still function, but the data integrity is compromised, leading to serious consequences.
Why It Matters:
Strong data integrity practices:
- Prevent fraud and unauthorized changes
- Ensure accurate and reliable information
- Maintain trust in digital platforms and systems
3. Availability (System Accessibility & Reliability)
Availability ensures that systems, networks and data are accessible whenever needed, supporting smooth operations and uninterrupted services.
Key Concepts:
- High server uptime and performance optimization
- Data backup and recovery solutions
- Disaster recovery planning
- Protection against DDoS and cyber attacks
Example:
If a hospital or banking system becomes unavailable due to a cyberattack or server failure, users cannot access critical services, this is a failure of system availability.
Why It Matters:
Ensuring high system availability:
- Supports business continuity and operations
- Reduces downtime and financial losses
- Ensures real-time access to critical services
The CIA Triad (Confidentiality, Integrity & Availability) forms the backbone of cybersecurity and data protection strategies. Together, these components ensure that data remains secure, accurate and accessible in today’s evolving digital environment.
Additional Components of Computer Security
Beyond the CIA Triad, modern computer security and cybersecurity frameworks include additional layers that strengthen data protection, access control and threat detection. Here’s the following:
1. Authentication (User Identity Verification)
Authentication is the process of verifying user identity before granting access to systems or data. It acts as the first line of defense in cybersecurity and access control systems.
Examples:
- Strong passwords and password security
- Biometric authentication (fingerprint, facial recognition)
- One-Time Passwords (OTP) and multi-factor authentication (MFA)
Why It Matters:
Authentication ensures that only authorised and verified users can access sensitive systems, reducing the risk of unauthorised access and cyberattacks.
2. Authorisation (Access Control Management)
Authorisation determines what level of access a user has after successful authentication. It is a key part of access control and data security management.
Example:
- Role-based access control (RBAC) such as admin vs user permissions
Why It Matters:
Authorisation ensures that users can only access relevant data and resources, minimising security risks and protecting sensitive information.
3. Monitoring & Logging (Security Tracking & Threat Detection)
Monitoring and logging involve tracking system activities and user behavior to detect suspicious actions and potential security breaches.
Examples:
- Login alerts and unusual activity detection
- Security logs and audit trails
Why It Matters:
Continuous monitoring helps organizations identify cyber threats early, respond quickly and strengthen overall cybersecurity posture.
4. Non-Repudiation (Proof of Actions)
Non-repudiation ensures that users cannot deny their actions or transactions within a system. It provides accountability and trust in digital communications.
Example:
- Digital signatures and secure online transactions
Why It Matters:
This component is essential for maintaining data integrity, legal compliance and secure digital transactions.
5. Physical Security (Infrastructure Protection)
Physical security protects hardware, servers and IT infrastructure from unauthorised physical access or damage.
Examples:
- CCTV surveillance systems
- Secure data centers and restricted access zones
Why It Matters:
Even the best digital security can fail without strong physical security measures, making it a critical part of overall cybersecurity strategy.
These additional components, like authentication, authorisation, monitoring, non-repudiation and physical security, enhance the core principles of computer security, creating a comprehensive and layered cybersecurity defense system.
Common Cybersecurity Threats You Must Know
Understanding the main components of computer security is essential, but it’s equally important to recognise the most common cybersecurity threats that put systems, networks and sensitive data at risk.
As digital adoption grows, cyber threats, data breaches and online attacks are becoming more frequent and sophisticated.
Top Cybersecurity Threats
Malware Attacks
Malware is one of the most widespread cybersecurity threats, designed to damage systems, steal data, or gain unauthorised access. It includes viruses, worms, spyware and trojans that exploit system vulnerabilities.
Phishing Scams
Phishing attacks trick users into revealing sensitive information such as passwords, banking details, or personal data through fake emails, messages or websites. It remains a leading cause of data breaches and identity theft.
Ransomware Attacks
Ransomware is a dangerous type of malware that locks or encrypts your data and demands payment for access. It can disrupt businesses, cause financial losses and compromise data security and system availability.
Data Breaches
A data breach occurs when confidential information is accessed or exposed without authorisation. This can result in loss of personal data, financial information and organisational trust.
Insider Threats
Insider threats come from employees or authorised users who misuse access privileges. These threats are often harder to detect and can lead to serious information security risks.
Security Across Different Digital Environments
Strong cybersecurity practices are essential across mobile, cloud and remote environments to ensure complete data protection and network security.
Mobile Security
Protect devices from cyber threats and malware attacks.
- Manage app permissions carefully
- Use antivirus and mobile security apps
Cloud Security
Secure data stored online with cloud security measures.
- Use data encryption
- Choose secure cloud platforms
Remote Work Security
Stay protected while working remotely.
- Use a VPN for secure connections
- Secure your home Wi-Fi network
Strong security across all environments ensures better data privacy, cyber threat protection and system safety.
Need More Details on Cyber Security Online Training Course
Ask Now
Key Security Technologies in Cybersecurity
Modern computer security and cybersecurity systems rely on advanced technologies to ensure strong data protection, network security and threat prevention.
1. Encryption : Encryption technology protects sensitive data by converting it into a secure format, preventing unauthorized access and data breaches.
2. Firewalls : Firewalls act as a barrier between trusted and untrusted networks, blocking malicious traffic, hackers and cyber threats.
3. Antivirus Software : Antivirus and anti-malware software detect, prevent and remove malicious software, viruses and ransomware attacks.
4. Data Loss Prevention (DLP) : DLP tools help prevent data leakage, unauthorized data transfer and information loss, ensuring strong data security and compliance.
These cybersecurity technologies form the backbone of modern IT security systems, protecting data, networks and digital assets from evolving threats.
Cybersecurity Career Scope
Cybersecurity careers are among the fastest-growing and highest-paying IT jobs, driven by rising cyber threats, data breaches and demand for information security professionals.
Top Cybersecurity Roles
- Cybersecurity Analyst (threat detection & risk management)
- Ethical Hacker (penetration testing & vulnerability assessment)
- Security Engineer (system security & infrastructure protection)
- Network Security Specialist (network defense & monitoring)
Salary Insight
Entry-level professionals in cybersecurity and information security jobs can earn competitive salaries globally, with strong growth opportunities across industries.
With increasing demand for cybersecurity skills, data protection expertise and network security knowledge, this field offers excellent career growth, job security and global opportunities.
Kickstart Your Cybersecurity Career with CC Learning App
In today’s fast-changing digital world, building strong cybersecurity skills is key to a successful and future-proof career. With increasing data breaches, cyber attacks and security threats, the demand for skilled professionals is growing rapidly.
Join CC Learning App, the best cybersecurity online training platform in Kerala and gain practical knowledge in information security, ethical hacking and network security.
Start learning today and step into a high-demand, high-salary cybersecurity career.
Download CC Learning App Today and Become a Cyber Security Specialist
Join Now
Frequently Asked Questions
1. What are the main components of computer security?
The main components are Confidentiality, Integrity and Availability (CIA Triad).
2. Which one is actually a component of computer security?
The correct answer is Confidentiality, Integrity and Availability.
3. Why is the CIA Triad important?
It provides a framework to protect data, ensure trust and maintain system performance.
4. What is the difference between authentication and authorization?
- Authentication verifies identity
- Authorization controls access level
5. What are common cybersecurity threats?
Common threats include malware, phishing, ransomware and data breaches.
Trending Updates